[Binary Exploitation]
Binary Exploitation & Memory Attacks
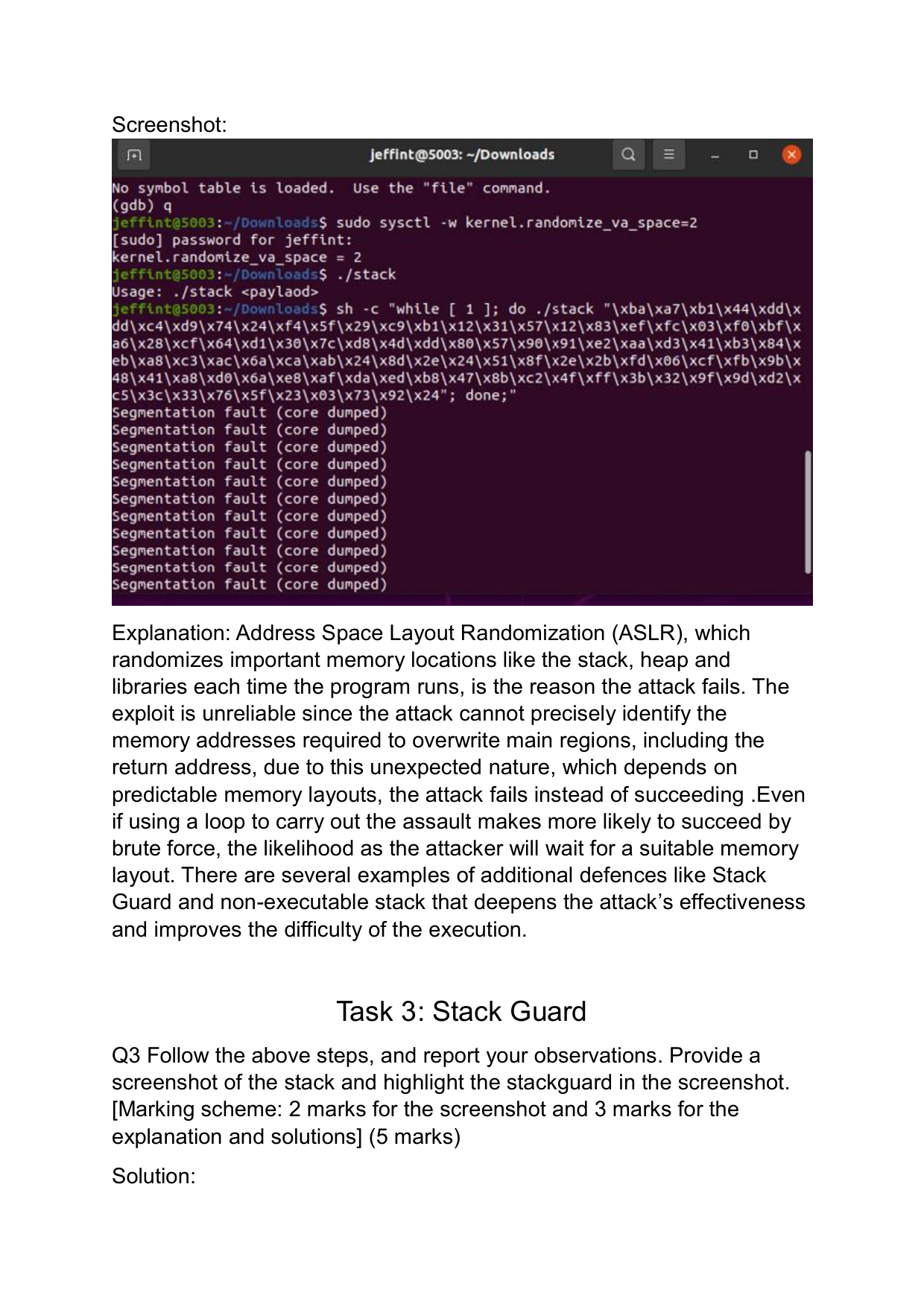
Deep dive into buffer overflow exploitation techniques including ASLR bypass, Stack Guard bypass, and format string attacks on vulnerable binaries.
[←] Prev[→] Next
TOOLS_USED:
GDBPythonpwntoolsROPgadget
KEY_FINDINGS:
- ▹Successfully bypassed ASLR using information leaks
- ▹Exploited stack-based buffer overflow for code execution
- ▹Demonstrated format string vulnerability exploitation
- ▹Achieved privilege escalation through ret2libc